Hackers are always looking for the easy way in, easy is what can be automated. Every Joomla website is managed from the administrator back-end. Starting point for accessing the administrator is as easy as adding /administrator to the domain name. Let the hacking begin!
So it is important to add an extra layer of protection on your administrator area. An extra layer that ensures you that only who is able to pass that layer should be able to see the back-end login page.
Basically there are two ways to add that extra layer of security, in this use case i will describe both and explain how (and why) ochSimpleFirewall handles protecting the administrator area.
Challenge: How do I block abusers from my administrator area?
So question is how do I protect my administrator area, while still being able to have external support (extension developers, etc.) access the site to do their job.
As said, there are multiple ways of protecting your administrator area:
- obfuscating / hiding the administrator page with a 'query' parameter, like [mydomain/administrator/?secret
- protecting your administrator area on a web server (Apache) level
Solution: New ochSimpleFirewall Administrator Area Protection
Starting with version 1.5.0 ochSimpleFirewall has build in support for protecting your administrator area on web server level (apache). This means that when you visit [mydomain]/administrator, your webserver will prompt you to login with login / username BEFORE anything (the Joomla administrator area) is loaded!
The reason why using server level protection and not protection via obfuscation is two fold:
- Obfuscation is NO security
- when DDOS-ing your administrator area, obfuscation will not help as the load on the server will become to high as it is Jooma servicing every access attempt instead of every access attempt being blocked before load is put on the web server.
Some time ago my website was under a DDOS atttack, the site was so heavily loaded with requests on my administrator area, that the whole website broke down and stopped responding. I was unable to login to Joomla myself and the only thing i could do was login to my hosting provider's control panel. The first thing i did was add a .htaccess / .passwd protection on my administrator directory. Within a second, the load on the server dropped to nearly zero, allow my customers to visit the site again and me to login to the site again to see if there was any damage done. So although the solution where I had hidden my administrator area with a query key (like AdminExcile does) took care of the hackers not being able to login, it didn't take care of my site going down and by doing so expose invaluable information to hackers. Obfuscation is NO security and protecting your administrator area should be done on a server level!
So basically what ochSimpleFirewall does is add industry standard .htaccess and .passwd protection to your administrator directory, enforcing somebody to first successfully login on Apache level before the administrator login page is displayed. This kind of protection automatically protects ALL of the administrator area independent of how it is accessed. And this is important as most likely your backups are stored in the administrator area as well.
ochSimpleFirewall let's you add multiple login names / passwords to the protection. This means that every support company or even administrator can have his own set of login credentials. So no more sharing your username password and after the job is done changing the password again. You can just give a support employee his own, temporary, login name.
Because the protection is on web server level, it is independent of Joomla or ochSimpleFirewall. So even if a hacker is able to stop ochSimpleFirewall or 'break' your Joomla installation, your administrator area and files are still protected!
Result: Best Practice protection, less load and less hustle when sharing credentials / secrets
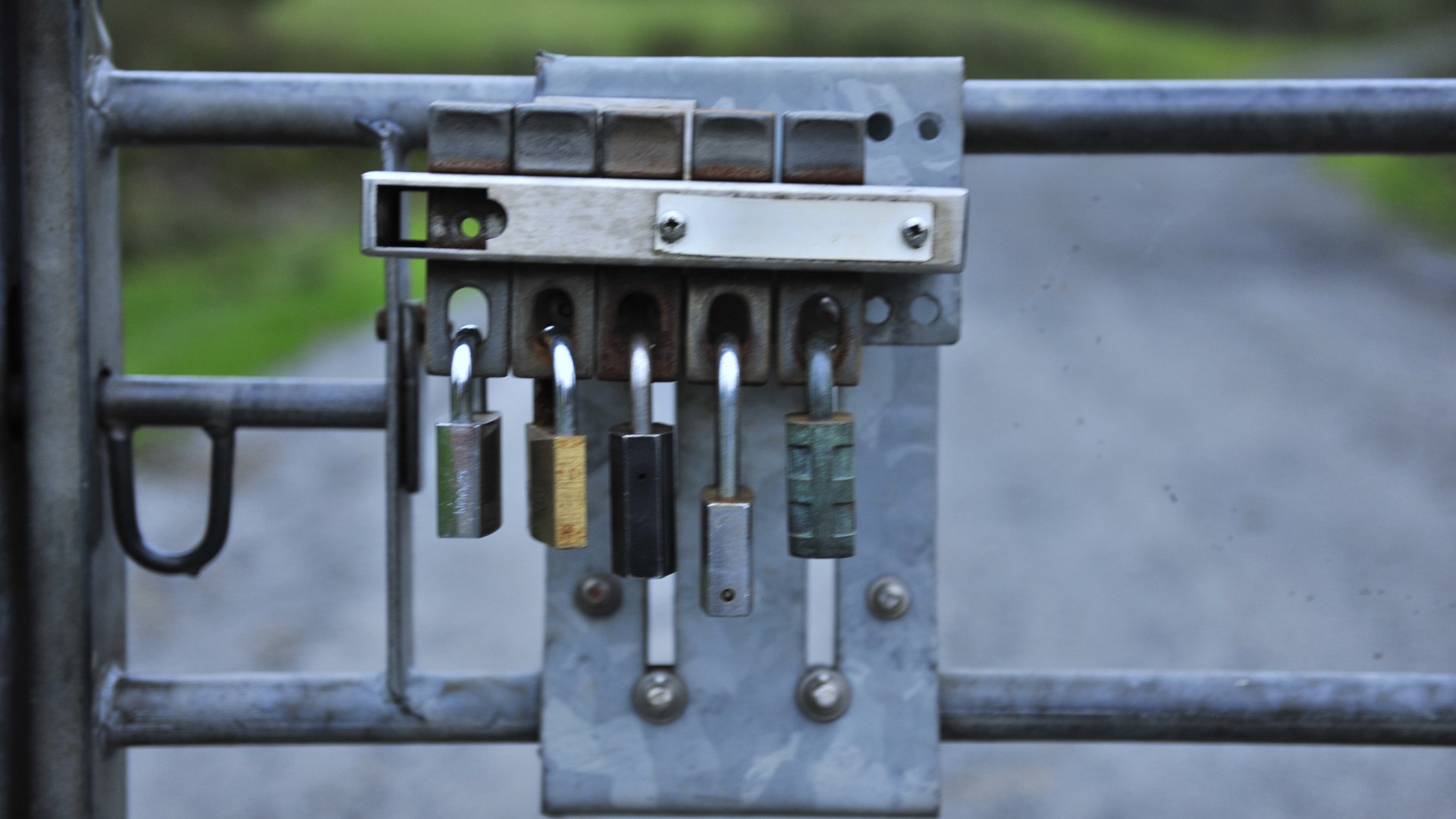
Image by Ray Jones: Locked Gate